20+ SAMPLE Employee Confidentiality Agreement
-

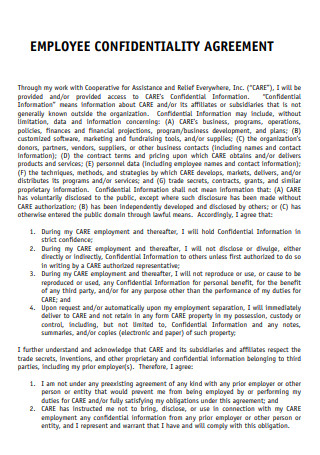
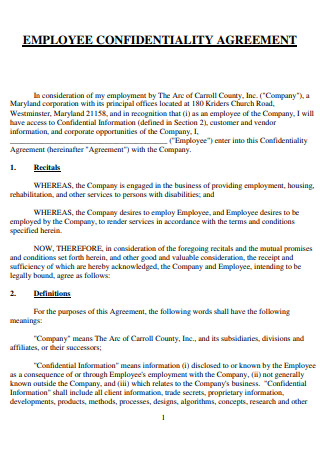
Employee Confidentiality Agreement
download now -
Employee Confidentiality and Non Disclosure Agreement
download now -
Employee Confidentiality and Non Solicitation Agreement
download now -
Employee Confidentiality and Non-Compete Agreement
download now -
Employee Privacy and Confidentiality Agreement
download now -
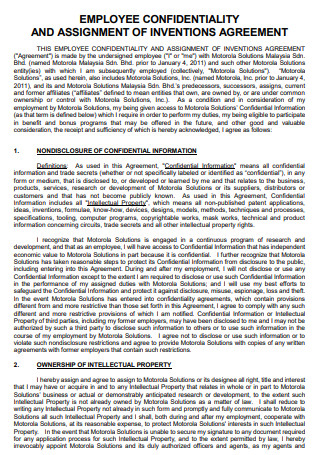
Employee Confidentiality And Assignments of Inventions Agreement
download now -
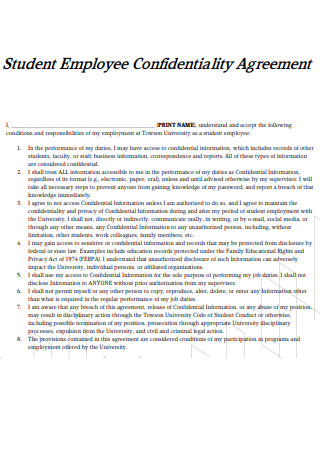
Student Employee Confidentiality Agreement
download now -
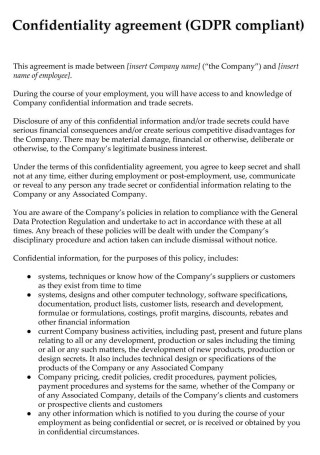
Employee Confidentiality Agreement Example
download now -
Basic Employee Confidentiality Agreement
download now -
Employee Reciprocal Confidentiality Agreement
download now -

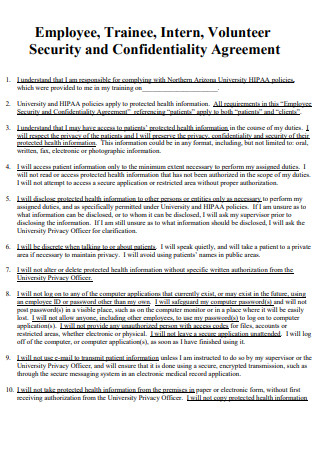
Employee Intern Confidentiality Agreement
download now -
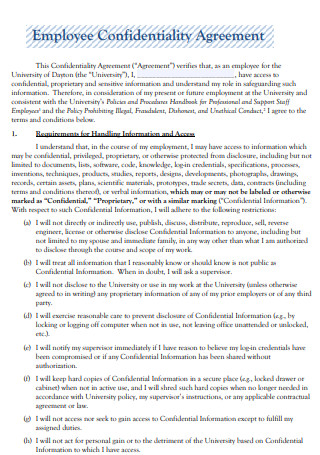
University Employee Confidentiality Agreement
download now -
Non-Employee Confidentiality Agreement
download now -
Employee Conflict of Interest Confidentiality Agreement
download now -
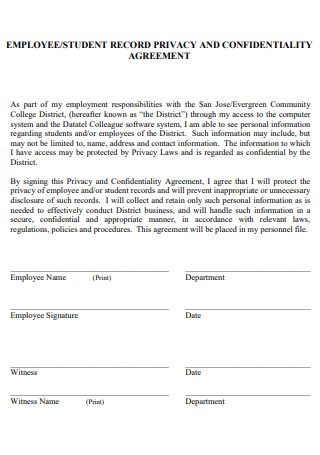
Employee Record Privacy Confidentiality Agreement
download now -
Employee Security and Confidentiality Agreement
download now -

Employee Confidentiality Agreement and Assignment
download now -
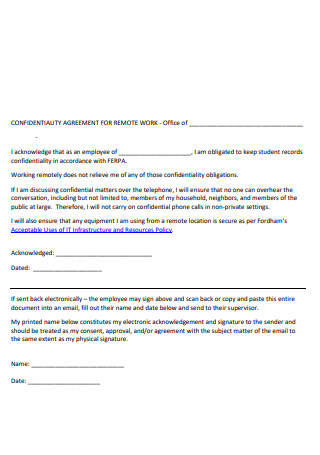
Employee Confidentiality Agreement for Remote Work
download now -
Employee Confidentiality Agreement Template
download now -
Standard Employee Confidentiality Agreement
download now -

Formal Employee Confidentiality Agreement
download now
FREE Employee Confidentiality Agreement s to Download
20+ SAMPLE Employee Confidentiality Agreement
an Employee Confidentiality Agreement?
Benefits of Confidentiality Agreement
Tips in Protecting Your Confidential Information
How To Protect Employee Sensitive Records
FAQs
Are confidentiality agreements with employees enforceable?
Who has the authority to create a confidentiality agreement?
Is human resource information private?
What Is an Employee Confidentiality Agreement?
When you need to protect data and techniques, this legal document can be utilized to ensure that your staff does not divulge your confidential information to others. Competitors, hackers, and even unrelated organizations may attempt to replicate your procedures, access your data, or steal the approach you spent so much time developing and implementing. A confidentiality agreement with your employees provides further protection by preserving your knowledge and preventing your staff from disclosing your secrets to the competitors. While an employee confidentiality agreement is designed to protect your employees, an equivalent document can be used to cover independent contractors; the format, material, and protections supplied are identical; the audience is simply different. According to statistics, 72%of employees are willing to share sensitive and confidential data or regulated firm information.
Benefits of Confidentiality Agreement
Employers frequently face the challenge of striking the right balance between protecting the business and satisfying employees. When management needs employees to sign a non-competition, non-disclosure, or confidentiality agreement, this issue may come to light. When a company weighs its confidentiality agreement choices, it should understand why they are necessary and what purpose they serve.
Tips in Protecting Your Confidential Information
In today’s corporate world, sensitive information such as client lists, proprietary technology, pricing information, and marketing plans are vital business assets that might be compromised if not handled appropriately. Exiting employees who opt to work for a competitor are a significant source of exposure. Also, there is a risk when confidential information is shared to negotiate a business contract, and the negotiation fails. Here are seven recommendations to assist you in safeguarding personal information:
-
1. Proper Labeling
If a business does not take necessary precautions to preserve its sensitive information, legal protection may be lost. Additionally, labeling confidential information acts as a practical deterrent to someone abusing secret information. Labeling can be found on both electronic and paper documents. A label may read: ” ABC Corp.’s confidential information and property. No part of these records may be duplicated, used, or disclosed without ABC Corp.’s explicit consent.”
2. Employers should include non-disclosure provisions in employee contracts.
Employees with access to confidential information should sign an employment contract that includes non-disclosure provisions. If a business has sensitive secret information, it should be mentioned in the agreement. When an employee’s job ends, they should be required to hand over confidential information. Although enforcing non-competition rules in an employment contract might be extremely difficult, confidentiality provisions are often legally enforceable. While the law imposes specific confidentiality responsibilities on employees, confidentiality terms in an employment contract make it abundantly evident that the employer takes secrecy seriously and thus helps avoid legal and practical complications.
3. Examine other contracts for secrecy clauses.
Companies regularly get into contracts with service providers, such as consultants and IT service providers. Many standard form contracts generated by service providers do not include any confidentiality clauses in the customer’s favor. In these cases, it’s better to sign a separate confidentiality or non-disclosure agreement with the service provider or “bolster” the service provider’s secrecy clauses in the contract.
4. Restriction of access
A business that maintains sensitive information should exercise caution in restricting access to secret information to personnel who have a “need to know.” Thus, the corporation enhances its legal position and contributes to establishing a practical “roadblock.” Documents should be kept locked in their physical form, and electronic versions should be password protected. Access to computers should be monitored. Monitoring “strange activity” may aid in bringing a legal claim against a departing employee if the situation warrants it.
5. Conduct a thorough review of third-party NDAs.
Third parties frequently supply businesses with “standard form” NDAs. After a period, they may appear to be identical, although there are occasionally significant differences. For instance, an NDA may require that information qualify as confidential. It must be identified as such in composing at the time of disclosure. If the disclosure is made orally, the information’s nature must be confirmed in writing within a specified time following exposure. This commitment can be highly demanding for a corporation that exposes secret information, and as a result, the NDA’s requirements might easily be overlooked. For a business disclosing private information, the best method is for the NDA to provide that all non-public information supplied is confidential regardless of whether it is designated confidential or in what form it is disclosed.
6. Notify the new employer if necessary.
Suppose a corporation is particularly worried about a departing employee working for a rival. In that case, it may send a letter to the new employer outlining the former employee’s legal obligations regarding the previous employer’s sensitive information. The letter frequently has a “legal chilling effect” on competitors seeking to actively or indirectly induce a new employee to disclose secret information about a previous employer.
How To Protect Employee Sensitive Records
You may be required to collect sensitive employee information during the working relationship, ranging from birth to Social Security Number (SSN) to medical data. As an employer, you need to protect this type of information. The following are seven tips for protecting sensitive employee data:
-
1. Formalize your policies and procedures.
Create a comprehensive data security policy outlining the types of sensitive information that the business will safeguard and the methods by which the business will protect such information. Declare that employee data will be collected only for legitimate company objectives and instruct employees to notify you immediately if they feel someone has accessed protected information without authorization. Also, declare that illegal copying, transferring, accessing, or using sensitive employee information is punishable by a penalty, including termination.
2. Securely store records.
Adopt administrative, technical, and physical precautions to ensure the security of personnel records. Paper records should be kept in a secure area with access restricted to a single individual who is primarily responsible for file maintenance. Electronic records should be encrypted, password-protected, and stored securely. Conduct regular evaluations of electronic systems to ensure that new technologies and viruses do not jeopardize security.
3. Adhere to recordkeeping regulations and restrict access.
Observe all applicable federal, state, and local recordkeeping and privacy requirements and preserve information only as long as necessary. Apart from specifying which documents must be stored and how long, these statutes may also set how records must be retained. For example, the ADA requires companies to separate employee medical information from personnel files and restrict access to these records. They are additionally limiting access to those who need the information. Managers, for example, should have access to just performance data, such as attendance records and performance reviews.
4. Conduct investigations into instances of illegal access.
Suppose you discover that someone may have accessed employee records without authority, whether intentionally or unintentionally, do an immediate investigation. Following the inquiry, assess whether changes are necessary to increase employee record protection and whether disciplinary action is necessary. Employers may be required by state or national law to notify state regulators or impacted persons and take specific other procedures in the event of illegal access or distribution of personally identifiable information. Conduct a review of applicable statutes to ensure compliance.
5. When feasible, avoid using SSNs.
To avoid identity theft or other forms of fraud, take reasonable precautions to prevent transferring, printing, or using employees’ Social Security numbers wherever possible. Consider issuing each employee an employee identification number that may be used as a unique identifier on time cards and personnel files. Numerous jurisdictions have enacted explicit legislation limiting employers’ usage of SSNs.
6. Properly dispose of records.
Employers must generally dispose of all personnel records to not be read or rebuilt or at the end of the retention period. Examples include burning, pulverizing, or shredding the documents so that the information cannot be read or reconstructed, ensuring the demolition or removal of electronic media containing employee information, and contracting with a reputable third-party vendor to dispose of the records correctly and under federal regulations.
7. Conduct training
Employees and supervisors should be educated about your company’s data security policies. Additionally, employees with access to sensitive information should be instructed on the company’s procedures and processes to prevent unauthorized access to personal information, respond to security breaches, and appropriately dispose of employee data. The training should include famous identity theft and hacking techniques used by identity thieves and hackers to obtain sensitive information, such as social engineering and phishing.
FAQs
Are confidentiality agreements with employees enforceable?
In general, secrecy agreements are enforceable if they adhere to the contract’s available standards.
Who has the authority to create a confidentiality agreement?
It establishes a contractual relationship between the two parties who sign it. However, the agreement must be signed by the appropriate parties. For instance, if one of the parties is a corporation, the corporation’s signature will be limited to a few individuals – often two Directors or a Director and the Secretary.
Is human resource information private?
Human resources must protect confidentiality regarding management or business information that is not accessible to nonmanagement workers or external parties. Confidentiality is also crucial for company investigations, performance evaluations, and disciplinary procedures.
Because an employee confidentiality agreement is enforceable in court, it is prudent to seek advice from a legal advisor or a professional in the industry before creating one. Ensure that the deal has all the necessary information. However, if specific information is not required to be shared, the agreement does not include it. By segmenting the agreement into distinct paragraphs, it becomes more readable. We offer a variety of employee confidentiality forms to fit the needs of firms in a variety of industries. These are easily customizable and can be printed out for immediate use. Compatible with all operating systems, we welcome your feedback and modify our forms to meet your specific requirements.
