30+ Sample Security Management Plan
-
Information Security Management Plan Template
download now -
Security Operations Management Plan Template
download now -
Hospital Security Management Plan
download now -

Basic Operational Security Management Plan
download now -
Physical Event Security Management Plan
download now -

Facility Security Management Plan in PDF
download now -
IT Security Guard Management Plan Review and Approval
download now -

Safety and Network Security Management Plan
download now -

Business Model Security Management Plan
download now -
Standard Roadmap Management Plan
download now -

Emergency and Security Controls Management Plan
download now -
Hotel Security Risk Management Plan
download now -
Beyond Security Action Management Planning
download now -
Initial Security Structure Management Plan
download now -

Cyber Site Security Management Plan
download now -

Information Security Healthcare Management System Planning
download now -
Printable Organization Security Management Plan
download now -

Simple Security Maintenance Management Plan
download now -

Security Approach Flow Project Management Plan
download now -

Cyber Security Data Management and Information Plan
download now -
Community Health Safety and Security Incident Management Plan
download now -

Cyber Security Supply Chain Risk Management Plan
download now -
Sample Security Management Plan
download now -
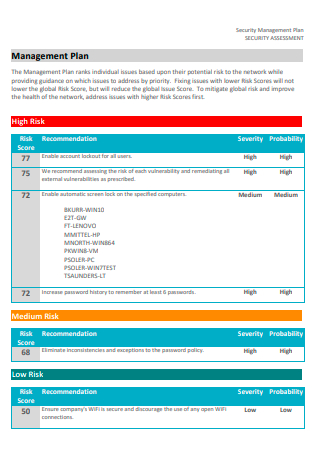
Security Assessment Management Plan
download now -
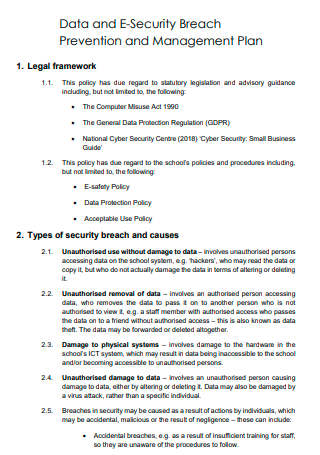
Data and E-Security Breach Prevention and Management Plan
download now -

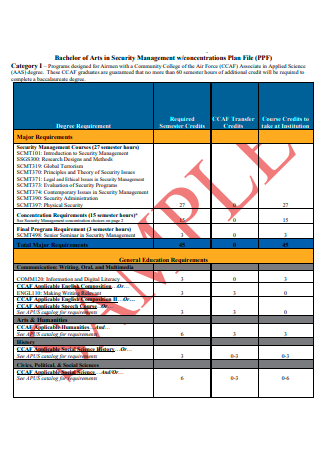
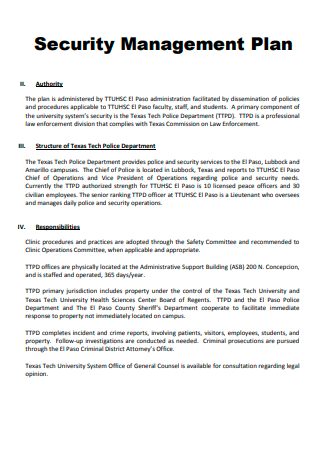
Security Management Plan Example
download now -
Formal Security Management Plan
download now -

Staff Safety Security Management Plan
download now -
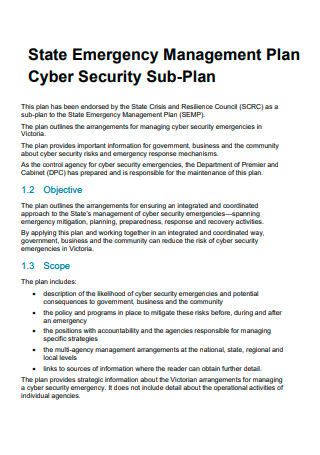
Cyber Security Emergency Management Sub-Plan
download now -
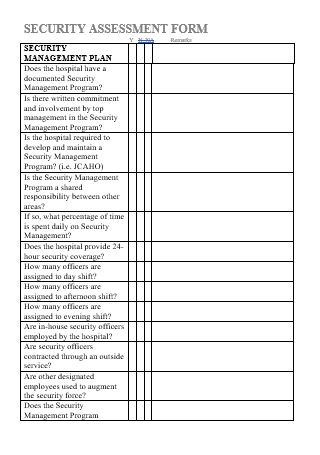
Security Management Assessment Form Plan
download now -
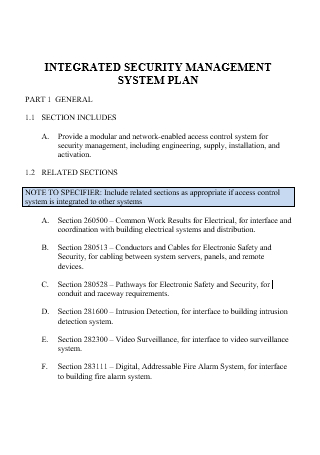
Integrated Security Management System Plan
download now
FREE Security Management Plan s to Download
30+ Sample Security Management Plan
What Is a Security Management Plan?
Components of a Security Management Plan
How To Create a Proactive Security Management Plan
FAQs
What does a good security management plan include?
What is a safety management plan?
How do you implement a security management plan?
What Is a Security Management Plan?
A security management plan provides a comprehensive framework that indicates all the necessary functions leading to organizational security. The security management plan aims to manage, staff, guide, and control corporate safety plans and protocols. It serves to inform internal security personnel and external stakeholders that include the board of directors, executives, and managers of security processes in the organization. It is critical to be aware that the security management plan does not provide explicit instructions or functions to follow. Instead, it serves as a guide to a procedure that utilizes and incorporates numerous and diverse operations for company protection. The security management plan is a critical component of many security strategies for organizations and industries. It is the responsibility of security managers to initiate and further develop security management plans to protect organizations from internal and external threats. Setting up a security plan helps with security risk assessments and hazard assessments for better and more efficient strategies to apply to potential hazards.
According to the gathered data in Statista about cybercrime breaches on record from 2005 to 2020 published by Joseph Johnson in March 2021, an occurrence of over one thousand cases of security data breaches during 2020 happened in the United States. During these data breach events, over 155.8 million individuals were affected. These include data exposures of confidential and sensitive information about the users.
Components of a Security Management Plan
Before writing a security management plan, you must know what goes into it to make a comprehensive document that the company can use. Since the system is a necessary tool to guarantee the safety and protection of the company, the elements that must be present are essential to the success of the security plan. Below are the components that must reflect in it.
How To Create a Proactive Security Management Plan
One of the problems with security and safety planning is that organizations tend to be more reactive than preventive when it comes to threats. Predicting possible risks and trying to prevent them from happening will prove to be more effective. Below are helpful steps in writing a security management plan for your organization.
-
1. Identify Possible Threats
Together with the members of the security management team, relevant personnel and entities, classify and highlight potential risks for the plan. Each member must consider scenarios in line with the roles and responsibilities and indicate possible threats, events, and situations. During this step, encourage individuals to be active in discussing risks, and ideas must be available for consideration. The security management manager will include and finalize the list of items for inclusion in the plan.
-
2. Evaluate and Assess the Threats
Organize the list of possible hazards and organize them according to likelihood and gravity. The compiled information is often called a risk register. While the risk register is not to be a part of the whole, it is a document that needs editing throughout the planning process. Communication is a big contributor to the success of a proactive security management plan.
-
3. Assign Individuals Responsible for Handling Specific Threats
Assign team members with the responsibility to oversee the risk, creating a priority list with descriptions of the resources you need to mitigate and prevent it. Designate individuals who are part of implementing emergency action plans. Uphold risk ownership in the security management plan to guarantee that there is someone who looks after the problem while resolving them efficiently.
-
4. Develop Preemptive Protocols
Together with the project manager, the team members assigned to each risk work together to develop appropriate responses when the threat becomes dangerous. Decide whether to avoid, transfer, mitigate, or accept the threat as necessary. In avoiding, you can change current plans and approaches to eliminate the hazard. When transferring, the member responsible for handling the task assigns it to someone else, whether within the team, organization, or external entities. Mitigation focuses on reducing the possibility of the threat being more harmful. Lastly, acceptance is a response that allows the risk to happen while facing the possible consequences afterward. Remember that the plan must be available to all team members to help identify all probable threats and the person to contact if it persists.
-
5. Continuous Monitoring of Threats
Aside from the identified threats at the beginning of the plan’s formation, there are new risks that arise. Since there are always new threats that are waiting to develop, the security management plan ensures continuous monitoring and controlling of hazards. Security management tracks and reports events that impact the organization to know when security management teams initiate response plans. Having a security management system in the company helps mitigate newer threats before they become harmful to the organization. Anticipating threats also encourages team members to continue finding possible risks and fitting solutions to combat them.
FAQs
What does a good security management plan include?
Every security management plan must have six essential elements to make them effective. It must have program management, prevention, preparedness, response, recovery, and training components.
What is a safety management plan?
A safety management plan is a important business document that provides the organization with strategies, techniques, and measures so organizations can continually identify and manage potential safety and health risks, reducing the possibility of accidents or illnesses.
How do you implement a security management plan?
Implement security management plans by determining and implementing assets, whether they are physical, information, or people. Afterward, perform a risk analysis and identify the effect it has on the organization. The next step is to specify and perform security practices. It is also essential to monitor whether violations are present and take the necessary actions. Lastly, reevaluate all assets and threats.
Individuals prioritize their safety above all else. Many homes, phones, laptops, personal computers, and bank accounts have passwords or codes to guarantee their security. The same applies to business establishments. Each company has safety and security protocols to protect company assets and revenue. No company will want to encounter threats and having a security management plan in place saves the time and effort to handle these types of situations. Download the sample security management plans available and start protecting your company today!
