21+ Sample Cyber Security Proposal
-
Cyber Security Guard Proposal
download now -
PhD Cyber Security Area Project Proposal
download now -
Cyber Security PhD Research Recommendation Proposal
download now -

Joint Cyber Security Business Plan Proposal
download now -
Cyber Security Security Awareness Proposal
download now -
Cyber Security Business Proposal Letter
download now -
Cyber Security Data Center Modernization Proposal
download now -

Cyber Security Proposal Form
download now -
Bachelor of Science Degree in Cyber Security Proposal
download now -
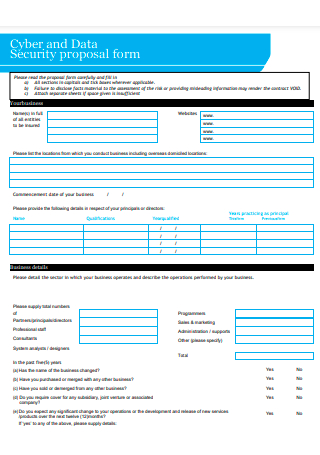
Cyber and Data Security Proposal Form
download now -

Cyber Risk and Security Proposal
download now -

Cyber Security Proposal in PDF
download now -
Cyber Security Products and Services Proposal
download now -

Cyber Security Insurance Proposal Form
download now -

Cyber Security Audit of Website Proposal
download now -
Cyber Security Services Proposal
download now -

Cyber Security Skills Research Project Proposal
download now -
Cyber Security Proposal Example
download now -
Cyber Security Act Proposal
download now -

Cyber Security Legislative Proposal
download now -

Standard Cyber Security Proposal
download now -
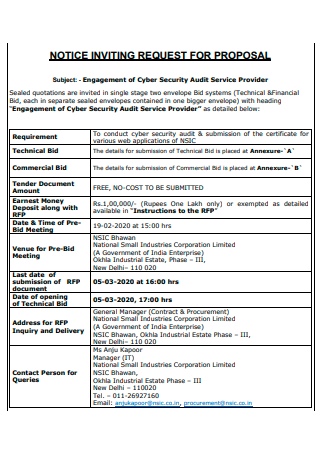
Cyber Security Audit Service Provider Proposal
download now
FREE Cyber Security Proposal s to Download
21+ Sample Cyber Security Proposal
a Cyber Security?
Benefits of Cyber Security Proposal
How To Develop a Cyber Security Plan
FAQs
What constitutes an effective cybersecurity strategy?
Is cyber security a source of stress?
What is the definition of personal security?
What Is a Cyber Security?
Cyber security is the practice of defending against malicious attacks on computers, computerized systems, networks, and data. The term “cloud computing” is used in various contexts, from business to mobile computing, and can be classified into a few broad categories. Cyber security is centered on the industry standard of confidentiality, integrity, and availability. According to statistics, 64% of businesses have been subjected to web-based attacks. 62%reported being a victim of phishing and social engineering assaults. 59% of companies have seen malicious malware and botnets, while 51% have encountered denial of service assaults. Privacy requires that data reports can be accessed only by authorized parties; integrity requires that information be added, altered, or removed only by authorized users; and availability requires that systems, functions, and data be available on-demand according to predefined parameters. Cyber security is primarily concerned with the use of authentication mechanisms.
Benefits of Cyber Security Proposal
As technology advances, the United States, like the rest of the world, continues to face the world’s fastest-growing form of criminality, cybercrime. Not only is the risk of becoming a victim of cyber-attacks increasing daily, but these attacks are also becoming more extensive and complex. According to the findings, businesses in the United States are currently losing more than 525 million dollars per year to cybercrime. Businesses of all sizes are targets and must be prepared to deal with this growing threat. Every business must now have a comprehensive cyber security action plan in place. While no solution can eliminate threats, a cyber security strategy can significantly reduce risks. Here are how it can benefit your organization.
How To Develop a Cyber Security Plan
Once you’ve understood cybersecurity best practices and conducted a risk assessment of your organization’s cybersecurity structure, you’re ready to begin developing your cybersecurity roadmap. How do you create a cybersecurity strategy?
Step 1: Recognize your organization’s cyber threat landscape.
To comprehend your cyber threat landscape, you must first study the types of cyber threats that your firm now confronts. Which types of risks are currently the most prevalent and severe in your organization: malware, phishing, insider threats, or something else? Have any of your competitors recently experienced significant occurrences, and if so, what types of dangers were involved? Following that, educate yourself on expected cyber threat developments that could harm your firm. Additionally, there is a growing problem with manufacturing and supply chain concerns, such as obtaining tainted components and using them internally or incorporating them into products you sell to customers. Understanding future dangers and the expected severity of each threat is critical for developing an effective cybersecurity plan.
Step 2: Determine your level of cybersecurity maturity.
Once you understand the threat, you must conduct an objective assessment of your organization’s cybersecurity maturity. Choose a framework for cybersecurity. Utilize it to determine your organization’s maturity across hundreds of distinct categories and subcategories, ranging from policies and governance to security technology and incident response capabilities. This evaluation should cover all of your technologies, from traditional information technology to operational technology and cyber-physical systems. Then, using the same cybersecurity framework, determine where your business should be in terms of maturity for each of those categories and subcategories in the next three to five years. If distributed denial-of-service assaults are a significant danger, for example, you may wish to invest in particularly mature network security capabilities. If ransomware is your primary security concern, it may be critical to ensure that your backup and recovery capabilities are pretty mature. Your new strategic objectives are the maturity levels you’re aiming for.
Step 3: Establish Achievable Objectives
While it is admirable to set smart goals, attainable goals are more vital to your business than a lengthy list of ineffective policies and processes. While a cybersecurity plan should include all desired tasks, it is critical to prioritize genuinely attainable ones. Some businesses make targets for themselves at the start of the year to accomplish a task in six months, but they never complete it in less than a year. Begin with the fundamentals; simple, attainable goals. Bear in mind that cybersecurity policies serve as a reasonable basis for the remainder of your cybersecurity operations. Prioritize the most critical and high-risk areas first and get them out of the way.
Step 4: Maintain Records of Your Cybersecurity Policies
It is a well-known truth that small firms frequently run more through word of mouth and intuitive knowledge than books. Cybersecurity is one area where documentation of protocols, processes, rules, and procedures is critical. You can access a comprehensive toolbox compliant with cybersecurity best practices and policies by developing a cybersecurity plan. While creating these policies may seem like a mammoth task, some organizations are renowned for their technical and business writing ability. You may contract with any of these organizations.
Step 5: Evaluate Vulnerabilities
After you’ve completed all of the above, don’t forget to conduct a test report. It would help if you ascertained whether or not your cybersecurity strategy is effective. Waiting to learn about a cybercrime after it happened is both impractical and dangerous. As a result, validate your plan. How do you accomplish this? Once a year, contact a cybersecurity professional to conduct a comprehensive security evaluation to ensure that your project remains relevant, current, and successful. Certain corporations even engage ethical hackers to attempt system compromises. Because cyber-threats are constantly evolving, your computer security plan should as well. According to the analysis, 84% of finance, manufacturing, information technology, retail, government, telecommunications, and advertising have high-risk vulnerabilities. 58% of businesses have one or more hosts with a high-risk exposure with a publicly available exploit. For 10% of discovered vulnerabilities, publicly available exploits are public, which means attackers can exploit them even if they lack professional programming skills or reverse engineering knowledge. However, more than half of the vulnerabilities can be addressed simply by applying the most recent software upgrades.
Step 6: Maintain a record of your cybersecurity approach.
Finally, after management clearance is obtained, you must verify that your cybersecurity strategy is fully documented. This involves creating or updating risk assessments, cybersecurity plans, rules, guidelines, procedures, and anything else necessary to describe what is required or suggested to accomplish the strategic objectives. It is critical to define each individual’s responsibilities. As you write and update these documents, ensure that you receive active participation and comments from those who will perform the associated job. Additionally, you should take the time to explain to them why these changes are being made and how critical they are for them to be more accepting and supportive. Also, keep in mind that your cybersecurity plan will require you to update your cybersecurity awareness and training initiatives. Every employee has a responsibility to play in resolving security concerns and enhancing your enterprise’s cybersecurity program. As your risk profile evolves, your cybersecurity culture must adapt as well.
FAQs
What constitutes an effective cybersecurity strategy?
A cybersecurity strategy is a high-level plan outlining how a business will secure its assets in an asset list and mitigate cyber risk. Like a cybersecurity policy, the cybersecurity strategy should be a dynamic, breathing document responsive to the changing threat landscape and corporate environment.
Is cyber security a source of stress?
Cyber security can be a demanding job, much more so if the position involves incident management. A significant occurrence may require all hands on deck and working under time constraints to complete responsibilities. As a result, additional hours are needed to ensure the issue is contained. According to research, the United States experienced a total of 1001 data breaches in 2020. Meanwhile, over 155.8 million persons were impacted by data exposures during the same year – that is, the unintended disclosure of sensitive information due to inadequate information security.
What is the definition of personal security?
Personal security is a broad term that refers to the state of being secure when reasonable attempts have been made to dissuade, delay, and warn of impending crime. If such warning happens, summon aid and constructively prepare for the likelihood of crime. According to research, the rapid growth of the US security industry has resulted in a 350 billion dollar market, with 282 billion dollars spent on private security. Despite the current considerable market worth, it is expected that the numbers will continue to grow in the future years.
Creating and implementing a cybersecurity proposal is a continuous process that will face numerous difficulties. You must review and reassess your organization’s cybersecurity maturity regularly to determine how well you are progressing – or not progressing – toward your objectives. The sooner you discover a weak point in your organization, the sooner you can remedy it and catch up. Internal and external audits, testing, and exercises that model what would happen in different conditions, such as a significant ransomware event, should be used to track progress. Finally, be prepared to reconsider your cybersecurity plan in the event of a potent new threat. Security agility is becoming increasingly critical. Never be afraid to alter your plan as cyber threats and security technology evolve, as well as your firm acquires new types of assets that require protection.
