20+ SAMPLE Network Security Proposal
-
Network Security Proposal
download now -
Network Security Engineer Proposal
download now -

Network Security Assessment Proposal
download now -
Network Security Penetration Proposal
download now -

Network Security Evaluation Proposal
download now -

Network and Information Security Proposal
download now -
Network Security Services Proposal
download now -
Network Security New Course Proposal
download now -

Network Information Security Proposal
download now -
Wireless Network Security Proposal
download now -

Sample Network Security Proposal
download now -
Basic Network Security Proposal
download now -

Network Security Monitoring Proposal
download now -
Network Discovery and Security Proposal
download now -

Network Security Audit Proposal
download now -
Network Security Camera Proposal
download now -

Network Based Security Proposal
download now -

Network Security Monitoring Service Proposal
download now -
Network Security Proposal Example
download now -
Network and Web Application Security Proposal
download now -
Network Security Proposal Template
download now
FREE Network Security Proposal s to Download
20+ SAMPLE Network Security Proposal
What Is a Network Security Proposal?
Types of Network Security
Benefits of Network Security
How To Make a Network Security Proposal
FAQS
What Is the Importance of Network Security?
What Are the Various Types of Network Security?
What Is the Importance of a Network Security Proposal?
What Is a Network Security Proposal?
A network security proposal is a document that outlines the security methods or technologies that could aid in the prevention of potential internet threats. Most computers and devices have their own built-in network security system. However, it is critical for businesses to safeguard the integrity and security of their network and data. That is why a plan for network security is essential. It is typically managed by a company’s IT department. And will be updated on a regular basis to account for new possible threats.
Types of Network Security
There are various kinds of network security. That increases the prevention and help to avoid data loss and theft. Since most businesses and homes are already connected to the internet. It is even more critical to provide a protective barrier that can shield our data from those who wish to exploit it. And there are many people who do it solely for financial gain. The internet is a dangerous world, and if you don’t come prepared, you’ll be at a significant disadvantage. So, here are the several sorts of network security that can be used in a person’s business and home networks.
Benefits of Network Security
Network security safeguards sensitive data and information within a business. And in today’s digital age, that is extremely important and required. Furthermore, establishing a reliable network security system enables for more efficient operation. It aids in avoiding delays caused by cyberattacks or any other cyber catastrophe that puts data at risk. Every network security plan includes a risk assessment. To thoroughly examine each posed risk and determine how to safeguard the network from it. And one should begin to build a strengthened network security. Since the following are some of its most significant advantages!
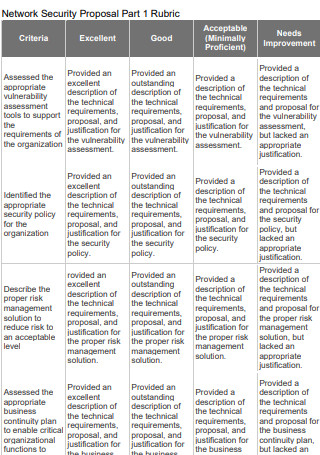
How To Make a Network Security Proposal
Network security is the most fundamental type of virtual protection that individuals and businesses can employ. It is also critical to be aware of how to protect your data and ensure internet security. Anti-malware and anti-virus solutions are extremely useful pieces of software to have on hand. Even if you are only concerned with the security of your own home, it is still beneficial to be aware about security in general. A network security proposal pdf can be used for either a corporation or a personal home. A research proposal for network security is similar. Let’s have a look at the steps to take down below.
Step 1. Identify the Purpose
When designing network security, it is important to consider how it will be implemented. A network security system at home would not be as comprehensive as one for a business. As a result, if you are tasked with developing a network security proposal for a client, it is critical that you understand where it will be used. Specifically, what is the purpose of network security? This is done to better determine which form of security measure is best suited to that specific environment.
Step 2. Threat Assessment
The second step in determining what type of security to use is to conduct a threat assessment. It is advisable to think about ordinary yet extremely severe dangers that could infiltrate your network. Malware and ransomware from downloaded files are prime examples. Or viruses distributed via email. It would be determined by what is required in the business or the nature of the activity. If staff check their emails daily, it is best to have a specific security against it. If it’s a home network, the most basic features are access control and firewalls. As well as parental control if there are children. Parents may be unaware that they can limit access without relying on settings inside the mobile applications they use.
Step 3. Develop Security Policies and Procedures
Following a threat assessment, the most natural next step is to develop strategies and policies to assist neutralize or isolate the threat. That is why it is critical that those working on this proposal are also familiar with network security solutions. Alternatively, knowledgeable on what kind of corporate culture and policies should be established for employees to follow. This could incentivize people to safeguard the system rather than potentially exposing it.
Step 4. Implement Security Controls
There are various types of security controls that can be implemented prior to using a network. This makes it easy to safeguard critical data and information. Implementing security controls may necessitate the use of certain technologies and programs. As a result, the needs must be identified in order to adequately prepare for implementation. As a consequence, the steps and tactics in the proposal are key. It is also advisable to seek the advice of an IT security professional who is well-versed in these matters.
FAQS
What Is the Importance of Network Security?
Network security is essential for a corporation to implement. It aids in the protection against any cyber assault or the prevention of prospective risks. As a result, it is important that these barriers are regularly updated in response to emerging threats. Just to assist reduce the likelihood of information being compromised and jeopardizing a company’s integrity, which could have financial ramifications.
What Are the Various Types of Network Security?
Access control and firewalls are the most fundamental elements of network security. Anti-malware and anti-virus apps are two more that consumers can download to improve their security. DDoS and DLP are two other types of network security.
What Is the Importance of a Network Security Proposal?
A network security proposal can assist in developing a clearer picture of how to implement security controls and measures. It also aids in the assessment and clarification of any potential hazards. It also contributes to the development of a more specific preventative intervention.
Nowadays, we need be cautious about our internet exposure. However, most devices already have rudimentary protection built in, such as a firewall. We must go above and beyond to safeguard our data against cyber assaults. Specifically, viruses, malware, and cyber-attacks. One approach is to propose a network security enhancement. As a result, the sample network security templates provided above can be used! Download it right now!
