3+ SAMPLE Security Bid Proposal
FREE Security Bid Proposal s to Download
3+ SAMPLE Security Bid Proposal
What Is a Security Bid Proposal?
What Is the Purpose of a Security Bid Proposal?
What Is the Bid Validity Period Used For?
How Is the Bid Validity Period Calculated?
What Happens When the Bid Validity Is About to Expire?
Elements of a Security Bid Proposal
How to Write a Security Bid Proposal
FAQs
What is data security?
Who is responsible for the security report?
Do a security proposal and a security report differ?
What Is a Security Bid Proposal?
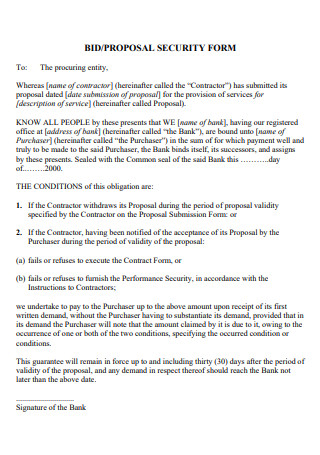
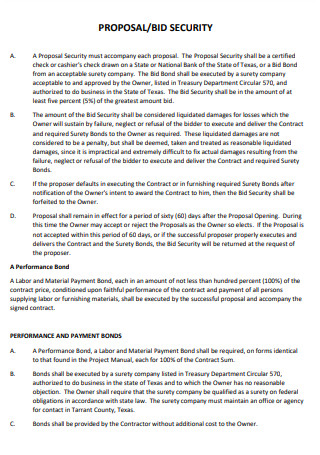
Contract security, sometimes known as bid security, is a type of risk insurance that is commonly employed in the construction business. Providing a bid bond with a construction bid ensures that the contractor will be obligated to sign the contract if the bid is granted to him in the future. The failure to sign the contract by a bonded contractor when it is given will result in both financial and civil consequences. These bonds are intended to protect the interests of the project’s owner or developer. A developer, a private firm, or a government entity can all be considered owners. Bid security aids in the reduction of erroneous bids and the reduction of wasted time for the owner.
Other templates are available on our website, and you can use them whenever you need them. They are as follows: security services proposal, employment contract, service contract, labor contract, construction proposal, staffing agreement, security company contract, work agreement, audit checklist, tenancy contract, bidding contract, and other similar templates are available. This post will not only provide you with templates but will also provide you with important information that you need to know in order to complete your template.
What Is the Purpose of a Security Bid Proposal?
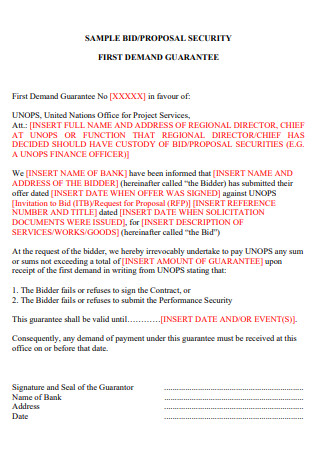
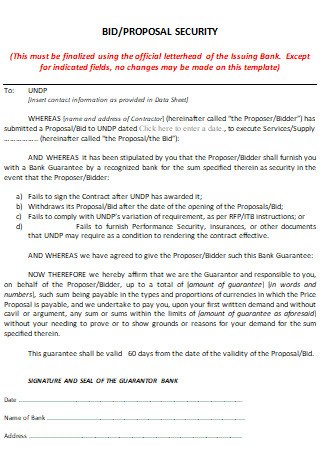
The bid security is meant to discourage bidders from withdrawing their bids because they would otherwise be liable to the customer for the amount of the bid security they have provided. It provides some reassurance to the client that the selected bidder will sign the contract or else forfeit their bid security if the contract is awarded to them. Firms that submit bids in response to a request for bids may be asked to provide bid security to protect their investment. It is frequently used in the procurement of products, construction projects, and non-consultant services. Despite the fact that it is uncommon for consultant services, it could be used if it is specified in the bidding documents and in the public procurement regulations.
As previously stated, the bid security amount can be established as a percentage of the bidder’s offer or as a percentage of the budget allotted for the procurement requirement, depending on the circumstances. Although it is preferable to set the bid security as a fixed amount or as a percentage of the bidders’ total bid rather than as a percentage of the allocated budget if the procurement method used does not permit the disclosure of the allocated budget, caution must be exercised when using this method. It is possible to prevent the budget from being revealed in an indirect or unintended manner by establishing the bid security amount as a percentage of the expected budget for the procurement demand.
What Is the Bid Validity Period Used For?
As previously stated, the goal of the bid validity period is to encourage bidders to agree to maintain their bid legally binding for a given number of days in order to convince the purchaser that their bid will not be modified during the defined period of time. As a result, it is critical for the purchaser to finish the selection process and execute the contract before the bid validity time expires.
How Is the Bid Validity Period Calculated?
It is necessary to have a good understanding of how long it will take from the date of bid submission or bid opening (as specified in the bidding documents) until a contract is signed in order to calculate the bid validity period. This period must be carefully estimated in order to reduce the likelihood of the need to extend the bid validity period; as a result, it is critical to understand the procurement timeline associated with the procurement method chosen and to manage the risks associated with the completion of the evaluation process, including the time required for bid evaluation and the time required by the approving authority to review and approve the evaluation report, with caution and care.
In the case of modest purchases, the bid validity time may range from 30 to 60 days. Depending on how long it is expected to take from the bid opening date until the contract is signed, the time frame for more complex procurements might be as long as 90 days or even more. Therefore, it is critical to calculating the bid validity duration carefully in order to complete the process before the time limit expires and prevent having to request an extension of the time limit.
What Happens When the Bid Validity Is About to Expire?
The bidders should be formally urged to consider extending their bid validity period if it is expected that the contract will not be signed before the bid validity period expires. When this occurs, bidders have the option to accept or reject the offer without incurring the loss of their bid security, and they may be authorized to adjust their bid price if this was specified in the bidding documents.
Elements of a Security Bid Proposal
Despite its crucial relevance to any firm’s performance, many firms disregard security. Affects both data and corporate property security Inadequate information security may cause poor performance due to competitors having access to corporate papers, data, and workflows. Thus, it is the firm’s job to provide adequate information security and encourage commercial property accountability. An easy-to-implement security solution for a corporation that protects business information and property from invaders is proposed here.
How to Write a Security Bid Proposal
Generally speaking, a security bid proposal is a document that contains thorough information regarding security protocols or measures that are required to manage threats and potential dangers. Security businesses write them and use them to coordinate with clients that hire them in order to develop an effective security service system for their clients. If you own and operate your own security company, you must have extensive experience in the creation of these proposals in order to be successful. Here are some pointers on how to go about creating them.
-
Step 1: Identify and Explain the Problem
In order for your client to be aware of the existing situation, The reality is that if they do not require security services, they will not seek them out on their own. To learn more about your client’s problem, conduct research, and interviews with them. This will serve as a guideline for how to formulate the Cyber Security Proposal, which will be based on the planning that occurs around it.
-
Step 2: Establish a Positive Public Image
To dispel any feelings of informality, portray the proper image of your company by stating how long you have been in business and never forgetting to mention the esteemed clients who have benefited from your services. This will increase people’s confidence in your company’s security services and their willingness to accept the contents of your proposal.
-
Step 3: Provide the Most Effective Solution
This is the meat of your security plan, and it should be read carefully. Once the problem has been identified, you should propose the solution that you believe will be the most effective in combating it. Example: If the issue is the presence of a large group of VIPs at an event, write about the need for event security in the venue to guarantee that everyone feels safe.
-
Step 4: Organize the Information You Want to Share
Once you’ve gathered all of your information for your proposal, choose a format that will make it easier to organize it all. Make certain that it contributes to your reader’s comprehension of everything in the letter. To learn more about security, you might look at checklists and security statements.
Developing a proposal to counter risks and keep your clients safe may appear to be a difficult task, but don’t allow that to deter you from taking on the challenge. Concentrate on one subject at a time and adhere to the guidelines outlined above to make this process far more manageable. In the event that you require additional guidance on how to construct a security proposal, please feel free to browse our other Business Proposal and Project Proposal templates for additional inspiration.
FAQs
What is data security?
It relates to safeguarding sensitive data held electronically. These strategies are commonly used by modern businesses that keep data online.
Who is responsible for the security report?
The security company’s front office normally creates and finalizes the security proposal. They know more about security than anyone else.
Do a security proposal and a security report differ?
While both include security, they differ in that they are planned ahead of time. Afterward, a security report is written.
It is critical to recognize that bid security is not the sole type of bonding instrument used on the majority of construction projects. In most cases, an owner who wants contractors to furnish a bid bond will also require contractors to provide payment and performance bonds. Once the contract is signed, the owner is protected by a payment bond in the event that the contractor fails to pay his suppliers and subcontractors on time. If the contractor fails to complete the task due to poor performance, financial difficulties, or insolvency, an owner is protected by a performance bond.